Welcome to Remedial Math 101
I’m looking at Google Maps. There’s a red pin on it. It shows where a Radio InfoWeb Listener is located. It shows a white pickup truck where a man is relaxing and listening on his Blackberry. This kind of tracking is now simple, automatic, and happens, perhaps, millions of times per second. It requires no more than an Internet connection and a web browser. The question is, is this acceptable?
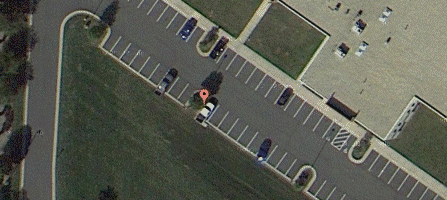
A man listening to an Internet Radio Station with a Blackberry is identified and located instantly via commonly available tools.
How was this done? Instantly and automatically. When the man’s phone contacted the audio server, it’s IP address became known, because it’s necessary to direct the audio stream to the stream player. When the IP Address is provided to Google, the telcom provider can be determined because IP addresses are issued in blocks (“NETBLKS”) to specific provider. The provider is then queried, and it instantly provides coordinates for the IP from its moble network. The cell tower providing the connection to the user’s phone has a multi-antenna array that allows it to geo-locate the source of the signal by comparing the phase relationships of the signal as it is received at each of the antennas.
The fact that it’s a Blackberry phone is known because the phone identifies itself when establishes the audio stream. The man may not be aware of many of these factors:
- That his telcom providers rats out his coordinates; perhaps even if he has expressly requested it not to
- That his phone rats itself out to the stream provider
- That cell towers triangulate his exact location
- That cookies are not involved
- That once you’re identified by an IP address, you’re associated with tons of tracking data that has been accumulated over time
The bottom line is, when you carry a cellular device that’s turned on, you may as well have a big target painted on your back, and another on the top of your head. You’ve been made. In real time. And as the title implies, you could be targeted by a drone, whether operated by the government, business, or criminal. In this surveillance society, it is becoming increasingly difficult to differentiate from the three when it comes to your personal security and safety.